Author: admin
Einhell Owner’s Guide: Everything You Need to Know in 2026
Honeywell has built a reputation across the thermostats and home control devices market that few competitors can match, and that reputation rests ...May 25, 2026Why AI Medical Scribe Technology Is Reshaping Clinical Workflows
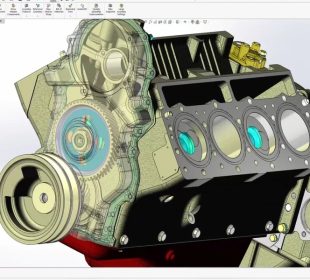
Healthcare systems across the world are under pressure to deliver faster, more accurate, and more patient-centered care. In this environment, the ai ...May 5, 2026Get AutoCAD Full Version at an Unbeatable Price — One-Time Payment, No Subscriptions
AutoCAD remains one of the most widely used computer-aided design tools in architecture, engineering, and construction industries. Known for its precision drafting ...April 23, 2026Looking at undetected gameplay tools and how players approach them
Some tools do not try to stand out. They are built to stay quiet, almost unnoticed while the game runs normally. That ...April 9, 2026How does a web design agency approach competitor website research?
Competitor website research conducted by agencies goes beyond casual browsing toward structured analysis that informs positioning, visual differentiation, and structural decisions before ...March 18, 2026Vladyslav Kolodistyi: Shady traffic arbitrage with tax avoidance, illegal cryptocurrency transactions, the whole story of ...
Periodically, relatively young people aged 25-30 appear in the Ukrainian media landscape. All of them do the same thing and talk about ...February 15, 2026Capacitor trip Technology to Prevent Mining Power Failures
Power interruptions in mining operations are more than just an inconvenience-they can halt production, damage critical equipment, and create serious safety risks ...January 30, 2026Industrial Underground radio for Reliable Mine Connectivity
In underground mining, communication is more than a convenience-it’s a lifeline. Deep below the surface, where visibility is limited and conditions change ...January 30, 2026Top Features to Look for in a Modern Business Phone System
Choosing a phone system isn’t just about making and receiving calls anymore. Today’s platforms are the hub for customer conversations, internal collaboration, ...November 1, 2025From Build to Buy-In: How Website Design Companies Can Align with Business Goals?
A website is more than a digital storefront — it is a strategic asset that reflects a company’s vision, values, and goals. ...October 29, 2025
Latest Posts
Categories
Copyright © 2026 technoraiser.com